When we talk about national security, we tend to focus on dazzling technologies—hypersonic fighter jets, laser weapons capable of disabling entire forces, or the most advanced semiconductor chips emerging from Silicon Valley. Yet a far more insidious and dangerous war is unfolding in plain sight. It is happening along the interstate highways we drive every day, at the busy ports of Charleston, South Carolina, and even inside the cabins of trucks transporting sensitive U.S. military equipment.
The recently proposed Trucking Security and CCP Disclosure Act of 2026 has begun to lift the veil on this hidden threat. The legislation would require any trucking company transporting Department of Defense cargo to certify that it has no ties to the Chinese Communist Party (CCP). It is, in many ways, a belated attempt to plug a critical vulnerability—one that could otherwise undermine the entire foundation of America’s military logistics system.
For decades, the United States has embraced globalization with open arms. In doing so, however, it has overlooked a dangerous reality: some actors exploit openness and trust as strategic entry points. While Americans believed they were making smart economic choices—outsourcing services and relying on cheaper foreign-made products—the CCP has been systematically leveraging these same systems to access, monitor, and potentially extract some of the most sensitive logistical and operational data underpinning U.S. national defense.

Behind the Steel Giants: The “Spy Eyes” of ZPMC Cranes
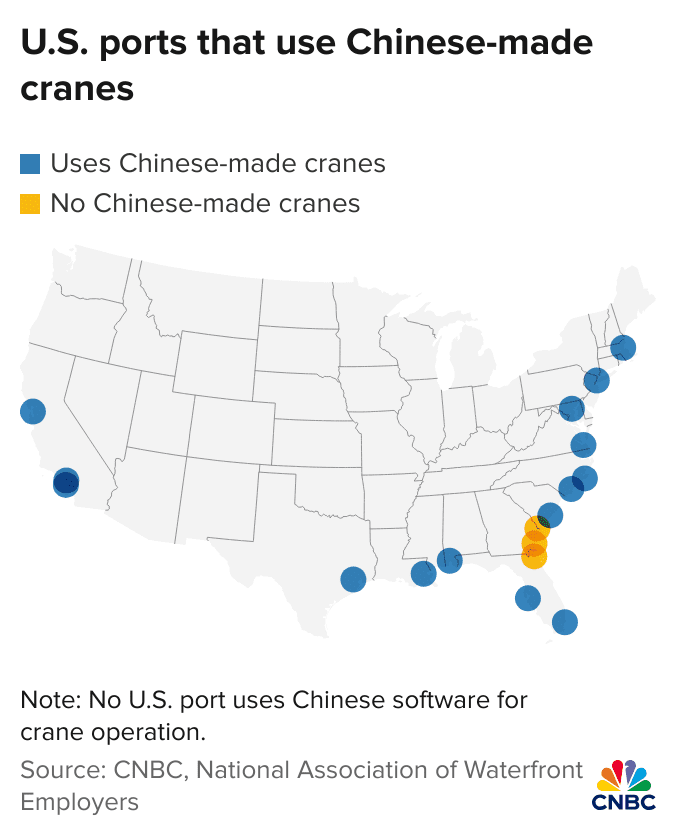
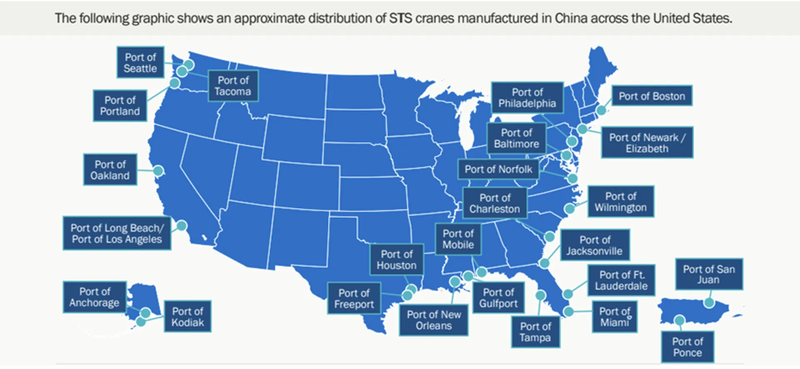
Across dual-use ports throughout the United States, hundreds of massive cranes manufactured by the Chinese state-owned enterprise ZPMC (Shanghai Zhenhua Heavy Industries) tower over critical logistics hubs. These steel giants handle roughly 80 percent of port cargo operations in the U.S. On the surface, they are symbols of efficiency and modern infrastructure. But a closer examination reveals a far more troubling reality: they may function as Trojan horses embedded at the gateways of America’s supply chain.
Between 2024 and 2025, congressional investigations uncovered that some of these cranes—delivered to U.S. ports—contained cellular modems that were not listed in official procurement contracts. These devices enable remote connectivity and, critically, can bypass internal port firewalls. This raises alarming implications. As U.S. military cargo—armored vehicles, munitions, or missile components—is loaded and unloaded, the cranes’ sensors can capture detailed data, including weight, dimensions, origin, and destination. Through these concealed communication modules, such information could potentially be transmitted back to servers under Chinese control.
Even more concerning is that the risk is not limited to passive surveillance. These cranes operate on software systems that could, in theory, be accessed or manipulated remotely. In a crisis or conflict scenario, a single command issued from abroad could disrupt operations across multiple U.S. ports simultaneously. This so-called “lights-out capability” would not merely slow logistics—it could paralyze critical nodes of military deployment, halting reinforcements before they ever leave the dock.
LOGINK: Beijing’s Global Logistics Web of Control
If cranes are the physical tentacles, then LOGINK (China’s National Public Information Platform) is the digital nerve system inside the CCP’s brain. Developed by China’s Ministry of Transport and directly funded by the Chinese government, this “free” logistics platform is designed to integrate global shipping data.
Using the Belt and Road Initiative as bait, the CCP has enticed dozens of major ports and thousands of logistics companies worldwide to connect to LOGINK—often at low cost or even for free. Once a port or freight forwarder adopts the platform, every bill of lading it processes, every import and export record of each container, and even precise data such as vessel draft and berthing time are automatically absorbed into the LOGINK system.

For the U.S. military, this is a disaster. Although military communications are encrypted, the vast majority of military supplies—food, fuel, spare parts—are handled through civilian vessels and commercial ports. Through LOGINK, Chinese intelligence agencies can use big data analytics to accurately estimate the U.S. military’s supply cycles in specific regions. If the flow of military cargo at a particular port suddenly surges, Beijing could know about U.S. movements at the same time as the Pentagon.
It is reminiscent of Samuel Jackson’s role in Kingsman, where free SIM cards are distributed worldwide under the guise of generosity, but in reality serve to control every user’s actions. The CCP’s LOGINK is not the product of a clever business strategy, but a political tool designed to gain the upper hand in global strategic competition.
The Remote Access Trap: Software-Defined Infiltration
The erosion of U.S. national security by the CCP is also reflected in its intense pursuit of control over operating systems. Many automated port systems and logistics management platforms operating in the United States rely on core code and maintenance access that remain in the hands of Chinese companies.
In multiple security audits, Chinese firms have been found requesting administrator-level remote access under the pretext of “software optimization” or “remote troubleshooting.” Once such access is granted, it creates an opportunity for CCP-linked cyber operators to implant backdoors within critical U.S. infrastructure.
This form of infiltration is even more pronounced in the trucking and ground logistics sector. Modern trucks depend on sophisticated fleet management systems (FMS) for scheduling, routing, and real-time tracking. If a company transporting U.S. military equipment relies on software tied to CCP-linked firms—or is backed by investors under Chinese control—then the precise location of every truck carrying Javelin missiles or drone components along interstate highways could effectively be visible to Beijing. Such visibility opens the door to route interception, or even the remote disruption of vehicle electronic systems through software commands—offering a low-cost, high-efficiency means of interference.
“Volt Typhoon” and the Destructive Prepositioning Within Critical Infrastructure
Do not underestimate the CCP’s infiltration of logistics networks—it is not a modern-day Cold War conspiracy theory. In light of the activities of the Chinese state-linked hacking group “Volt Typhoon,” the intent to penetrate and potentially disrupt critical infrastructure has already been demonstrated.
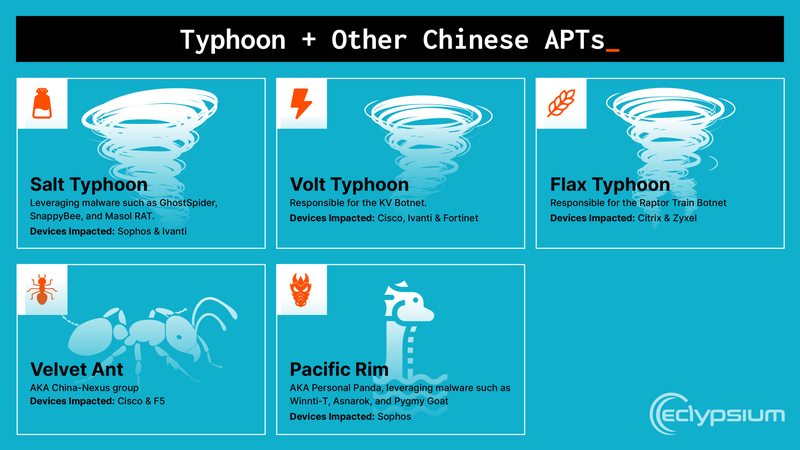
The U.S. National Security Agency (NSA) and the FBI have confirmed that Volt Typhoon does not operate like a conventional cybercriminal group. Its objective is not to steal credit card data or conduct ransomware attacks. Instead, it focuses on long-term persistence—embedding itself within U.S. communications, energy, water, and logistics systems. Its strategic goal is clear: to remain hidden until a moment of crisis, when pre-positioned malicious code can be activated to trigger widespread disruption across the United States.
Consider the implications. As trucking companies prepare to deliver critical equipment to ports, and cranes stand ready to load shipments, a single directive from a CCP authority could activate such latent capabilities. Power to port facilities could be cut. Truck navigation systems could be disabled. Cargo manifests within platforms like LOGINK could be altered, redirecting supplies to locations under adversarial control. This kind of coordinated, system-wide disruption would not require sinking ships at sea. Instead, it would paralyze the U.S. warfighting apparatus from within—by exploiting the very logistics systems operating on American soil.
Recognizing the Threat: The CCP’s Military-Civil Fusion Strategy
We must confront a fundamental misconception: the belief that Chinese companies are merely commercial entities. Under the National Intelligence Law of the People’s Republic of China, all citizens and organizations are required to “support, assist, and cooperate with state intelligence work.”
This means that companies such as Huawei, ZPMC, and any trucking technology firm receiving CCP subsidies—regardless of their size or sector—function, in essence, as extensions of the Chinese state’s security apparatus. When we allow these entities to penetrate our military logistics chain, we are effectively inviting a strategic adversary into the heart of our defensive infrastructure—and paying them to help transport our most critical supplies.
Rebuilding America’s Great Wall of Security
The Trucking Security and CCP Disclosure Act of 2026 is a signal of awakening. However, to counter the CCP’s comprehensive infiltration, a far more decisive strategy is required:
The price of freedom is constant vigilance. The CCP has demonstrated its willingness to exploit every gap in globalization to weaken the United States. If we continue to tolerate these “Made in China” vulnerabilities within our logistics and security systems, then when a real crisis arrives, we may find that our most critical strategic supplies are already in the hands of our adversary.

Now is the time to close these digital and physical gateways—and to reclaim control over the lifelines of national security.