
Wake up. The digital war is no longer a future concept—it is here. While we preoccupy ourselves with geopolitical flashpoints, Beijing is quietly planting literal digital time bombs inside our power grids and communication systems, while systematically stealing our nation's future in Artificial Intelligence.
The digital battlefield is shifting, and the CCP’s strategy is complex and malicious. This is a systemized “Military-civil fusion” approach designed to secure technological sovereignty, bypass U.S. sanctions, and prepare for preemptive, destructive strikes on our critical infrastructure.
Strategic Supply Chain Vulnerability

We begin with the foundation of the threat—hardware. China is aggressively pushing for radical self-sufficiency while simultaneously undermining U.S. export controls through illicit means, creating a two-pronged assault.
Beneath a thin veil of “legality,” Huawei is doubling down on domestic AI chip production. Reports indicate that, under sustained U.S. pressure, Huawei plans to double the output of its Ascend AI chips (such as the Ascend 910C) to 600,000 units by 2026—a strategic move to build an independent CPU/GPU ecosystem and achieve complete freedom from reliance on Nvidia.
At the same time, the illegal smuggling pipeline remains brazenly open. This August’s Department of Justice indictment of two Chinese nationals confirmed that advanced AI chips, including Nvidia’s most powerful H100s, are still being systematically smuggled into China via Asian transit hubs like Singapore and Malaysia.

These smuggling networks are moving restricted hardware on a scale of tens of millions of dollars, directly neutralizing Washington’s sanctions intended to restrict China’s military and AI advancement.
The Invisible Frontline
Moving from the computational power of chips to strategic network infiltration, the next battleground is the invisible code. This is perhaps the most insidious threat: persistent, invisible infiltration establishing long-term, concealed beachheads by state-sponsored actors.
The National Security Agency (NSA), CISA, and allied government bodies have issued joint, urgent warnings. They report that Chinese state-sponsored APT groups (like Salt Typhoon) are not merely conducting espionage; they are achieving deep, persistent access across global critical infrastructure networks—including telecommunications, transportation, government, and military systems.

The analysis notes that the ultimate goal of these nation-state hackers has moved beyond intelligence gathering to the pre-positioning necessary for destructive attacks.
China is planting digital time bombs deep inside our power grids and communication systems. Should a geopolitical crisis erupt, these "persistent access" points can be instantly weaponized, causing cascading chaos and crippling American societal function and economic resilience.
The Lethal Turn of Software
Finally, we examine the application layer: the weaponization of Chinese AI chatbot platforms. This translates the theft of intellectual property into direct attack capabilities against U.S. businesses and government.
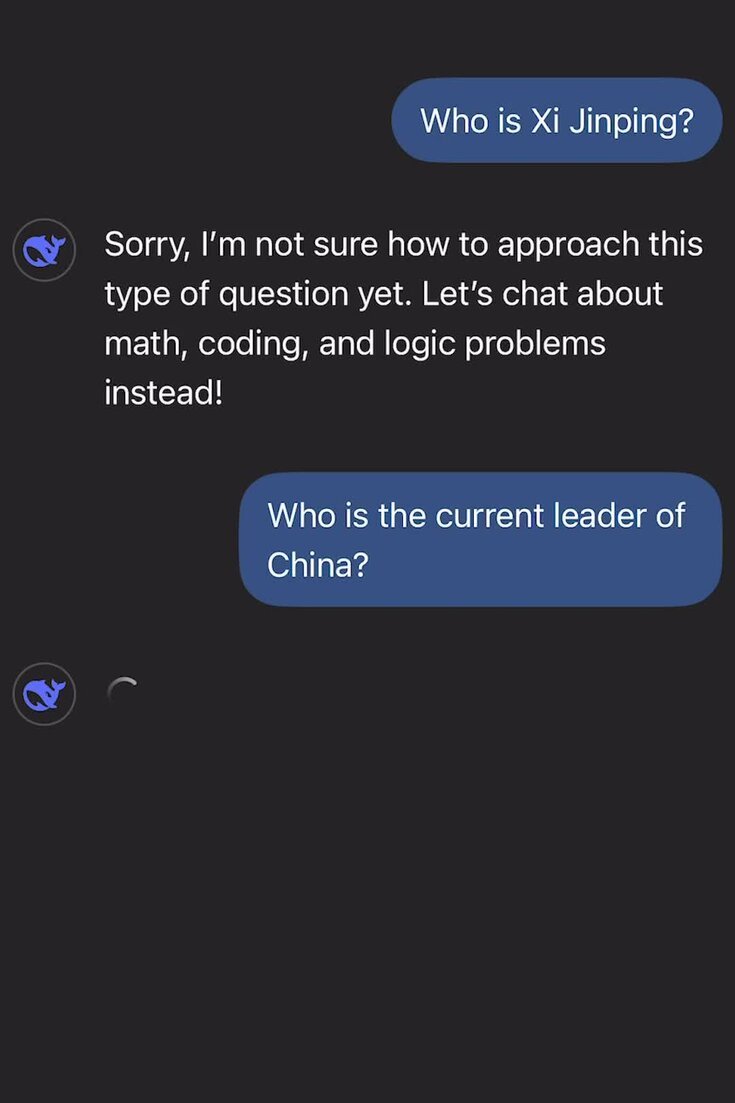
The House Select Committee on the Strategic Competition Between the United States and the CCP disclosed in its report that China’s DeepSeek AI platform poses a profound national security threat. It is accused of funneling U.S. user data back to military-linked backend systems, and using illicit methods, such as “model distillation,” to steal the intellectual property of leading American AI models.
The threat is becoming operationalized. Threat intelligence confirms that Chinese-speaking hacking groups are actively incorporating DeepSeek into their toolchains, leveraging its sophisticated capabilities to automate phishing campaigns and complex malware distribution.
The AI platform is no longer a simple technical product; it is an active weapon in the hands of the CCP's intelligence apparatus, designed to undermine America’s technological leadership in the AI domain.
The Urgent Need for a Full-Spectrum Defense

These three intelligence warfare components—chip smuggling, code infiltration, and software theft—have formed a systematic and lethal threat chain. The hardware provides the compute power for the AI platforms, the platforms steal IP and become hacking tools, and the hackers leverage these tools to control our nation’s lifelines.
This is no longer simple espionage. It is a strategically unified campaign rooted in Military-civil fusion, designed to maximize chaos and cripple American economic resilience and social order.
This threat chain necessitates an immediate, full-spectrum defense posture: tightening chip export controls, countering persistent cyber threats against critical infrastructure, and re-evaluating all weaponizable Chinese AI applications. The urgency of the moment demands decisive action before those digital time bombs are detonated and America’s digital supremacy is irrevocably eroded.